$ cd /projects/hacker-era
The Hacker Era — SLAE, OSCP, OSCE & DefCon 25
Certs: SLAE · OSCP (March 2017) · OSCE (May 2017)
PRE — Idea · Setup · Build
Goal: Become a professional hacker. For money, this time. I'd been hacking since before it had a career path. Reverse engineering software on the Amiga 500 and 2000 as a teenager. Writing 68k assembly in Masterseka assembler — which later became my DJ name, a joke that absolutely nobody ever got. Built entire AmiEx tools in assembly. Was interested in analyzing copy protection mechanisms in PC software. Direct memory access, compression algorithms, reverse engineering binaries — this was my playground before I ever touched a web framework. That early assembly work is why the current FPGA project feels so natural. Low-level thinking. Registers. Timing. Bit manipulation. The brain never forgot. The idea: take all that underground knowledge and make it legitimate. Get certified. Get hired. Wear the black hoodie professionally. Three certifications, one conference, one year. The hacker speedrun.
SLAE — SecurityTube Linux Assembly Expert
Found it on Coursera (or similar). It resonated immediately because it involved writing custom shellcode and creating your own encryption routines to evade pattern-based antivirus detection. Not "run a tool and read the output" — actual low-level code that has to fool other code. For someone who'd been writing 68k assembly since their early teens, x86 shellcode was a natural transition. Different instruction set, same mindset: you're writing code that operates at the boundary between software and hardware, where one wrong byte means a segfault and one right byte means you own the machine. The certification required building custom encoders, polymorphic shellcode, and demonstrating that your payloads could bypass signature-based detection. The kind of work that makes antivirus vendors nervous and penetration testers employable.
OSCP — Offensive Security Certified Professional
The infamous one. Offensive Security's flagship certification. The exam: 24 hours. A set of target machines. Hack them or fail. No multiple choice. No partial credit. You either break in and prove it, or you don't. The course (PWK — Penetration Testing with Kali Linux) covers everything: reconnaissance, exploitation, privilege escalation, pivoting, buffer overflows, web application attacks, post-exploitation. It's the most hands-on security certification that exists. Their motto: "Try Harder." I passed. Of course I passed. But it was tough, and I loved the intellectual challenge. Every machine is a puzzle. Every privilege escalation is a chess move. The 24-hour time pressure turns it into a marathon of lateral thinking under stress. Certified: 25th of March, 2017.
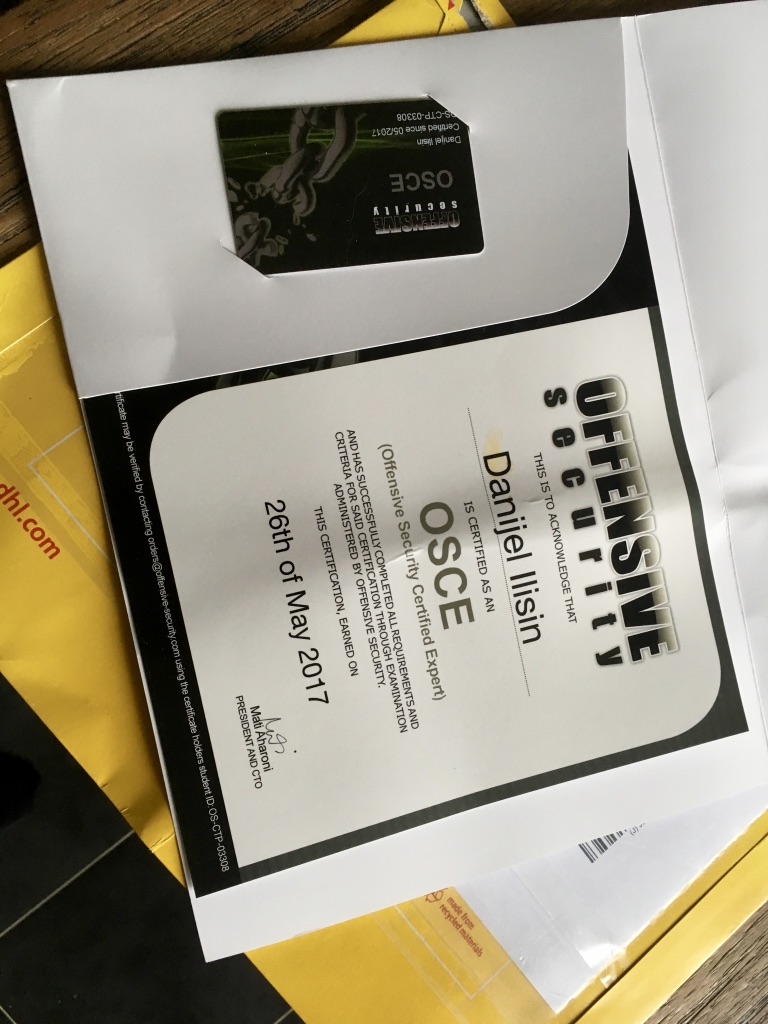
OSCE — Offensive Security Certified Expert
OSCP is for children. OSCE is the real deal. Two months after OSCP, I signed up for CTP (Cracking the Perimeter) — the advanced course. Custom exploit development. Advanced web attacks. Network-level exploitation. Writing your own exploits from scratch against real software with real protections. The exam: 48 hours. Not 24. Forty-eight. I finished in 24. And I'm still fairly sure I found a solution that was NOT the one they intended. Which, if you think about it, is the most hacker thing possible — solving the hacker exam in a way the exam designers didn't anticipate. Certified: 26th of May, 2017. OSCP to OSCE in two months. The speedrun was real.
The Certificates

DefCon 25 — Las Vegas, 2017
The pilgrimage. The biggest hacker conference on the planet. Caesar's Palace, Las Vegas. Flew there with my girlfriend and combined it with a California road trip. The expectation: a gathering of the world's most brilliant hackers. The underground made visible. Black hoodies and zero- days. The reality: a handful of truly skilled hackers surrounded by a million people marketing the shit out of "security." Corporate booths. Vendor swag. LinkedIn-grade networking. It felt like a trade show with better t-shirts. And me? Couldn't connect. Even among the nerds. I'm just not a conference person. Too many people, too much noise, too little depth. The hallway conversations were surface-level. The talks were hit-or-miss. The village demos were cool but crowded. Las Vegas itself was impressive. Caesar's Palace is an absurd complex. The desert heat. The casinos. The sheer excess of everything. Still wearing that DefCon 25 t-shirt. Right now, actually. But the conference itself taught me something important about the security industry: the "true" hackers don't attend conferences. They reverse engineer Chinese firmware in WLAN routers. They fuzz Android kernels looking for buffer overflows. The best ones are invisible. And they don't have a booth at DefCon.
POST — Learnings · Afterthoughts · Timeline
What happened:
I became a certified hacker. SLAE, OSCP, OSCE, DefCon. The
full stack. Then I looked at the job market and discovered the
gap between the fantasy and the reality.
The fantasy: wearing a black hoodie, finding zero-days, breaking
into systems, living on the edge of legal and illegal.
The reality: penetration testers spend 80% of their time writing
reports. Running automated tools. Filling out compliance
checklists. The pay is mediocre for the skill level required.
And the corporate security world is just as bureaucratic as
every other corporate world.
The actual elite hackers — the ones finding zero-days in
embedded systems, reverse engineering nation-state malware,
building custom exploit chains — they don't work at
consultancies. They work alone, or in small teams, and they
sell their work to governments and exploit brokers. That's a different world entirely.
So I filed the certs, kept the knowledge, and moved on. The
assembly skills came back 8 years later when I started writing
Verilog for the FPGA DAC. The low-level thinking never leaves.
The bit manipulation, the timing analysis, the register-level
reasoning — it's all the same muscle. Different language,
same brain.
The hacker era didn't become a career. It became a foundation.
Learnings:
- The OSCE 48-hour exam completed in 24 hours with an
unintended solution is the most "me" achievement on this
entire site. Solve the puzzle, but not the way they expected.
- The gap between "hacker culture" and "security industry" is
vast. One is driven by curiosity and intellectual challenge.
The other is driven by compliance frameworks and audit
reports. They share a vocabulary but not a soul.
- Conferences are for networking. The actual knowledge transfer
happens in CTF challenges, private IRC channels, and late-
night debugging sessions. DefCon taught me that the best
hackers are invisible.
- Assembly language learned on an Amiga 500 in the early 1990s
is still paying dividends in 2025 on an FPGA. Low-level
thinking is permanent infrastructure.
- "Masterseka" — the name of a 68k assembler for the
Amiga, my DJ name, and a joke that precisely zero humans
have ever gotten. Until now. You're welcome.
- The pattern: dive deep, master it, discover the real-world
implementation is boring, extract the knowledge, move on.
Music production (composing > mixing). Hacking (exploits
> reports). The 10% is always where the magic lives.
Timeline:
- 1990s: Amiga 500/2000. 68k assembly in Masterseka. Cracking
software. Reverse engineering. Building AmiEx tools. The
origin.
- 2000s-2010s: The knowledge sits dormant. Decades of web
development, startups, Rails. But the low-level brain is
always there.
- Early 2017: SLAE certification. Custom shellcode. AV evasion
through polymorphic encoders. The old skills, modernized.
- 25 March 2017: OSCP certified. 24-hour exam. Passed.
- 26 May 2017: OSCE certified. 48-hour exam. Finished in 24.
Unintended solution. Two months after OSCP.
- July 2017: DefCon 25. Caesar's Palace, Las Vegas. California
road trip with girlfriend. Conference disappoints. T-shirt
survives.
- Late 2017: Job applications. Discovery: pentesting = reports.
Pay = mediocre. The dream dies.
- 2025: The assembly skills return. FPGA DAC project. Verilog
is just a different assembler. The hacker era was never
wasted.
Status: Retired from offensive security. The certs gather dust.
The knowledge lives on in the FPGA project, where low-level
thinking is the entire job. The DefCon 25 t-shirt is still in
regular rotation. The black hoodie fantasy was always more fun
than the compliance reality. But the 48-hour exam in 24 hours?
That one stays on the wall.